Public health depends on information derived from monitoring population health status to identify community health problems and to diagnose and investigate health problems and hazards in the community. These depend on vital statistics and disease reporting systems, including for non-communicable diseases, injuries, risk factors, health care resources, utilization of resources, and special disease registries such as for cancer, birth defects, and many others.
Information technology and computerization allow data systems to be linked to assess the impact of health conditions and utilization of services providing vital information for epidemiological and economic analyses for policy development and decision making.
Internet of Medical Things devices continues to grow in variety and quantity to facilitate the monitoring process of population health status including investigating, diagnosing, and monitoring the vital signs of health hazards. the ability of this surveillance process to save lives and collect data poses an escalating challenge: Keep tabs on what’s happening with each one and determine whether any of their individual behaviors indicate a threat to their health.
Curabitur aliquet quam id dui posuere blandit. Lorem ipsum dolor sit amet, consectetur adipiscing elit. Pellentesque in ipsum id orci porta dapibus. Pellentesque in ipsum id orci porta dapibus. Vivamus magna justo, lacinia eget consectetur sed, convallis at tellus. Lorem ipsum dolor sit amet.
How secure are these devices?
Protecting a Wi-Fi enabled heart monitor or insulin pump, after all, requires a different approach than protecting a smartphone or laptop, as those devices are designed with built-in risk prevention to deter viruses and unauthorized users.
With the high use of IoT devices by people in a healthcare setting, healthcare service providers must make network monitoring a priority to ensure patient safety, the privacy of data, and continuity of care.
Standard anti-virus software does not run on most of them. So, it’s important to protect everything on the perimeter, to have tight controls internally and maintain network segmentation, and place a high emphasis on monitoring.
It is predicted that Eighty-seven percent of healthcare organizations will use IoT devices in some form on 2022. Among those already using IoT devices in 2021, 89 percent reported suffering an IoT-related security breach.
How do we ensure the security of these life saving IoT devices?
Network monitoring and diagnostic tools are designed to alert users, via alarms and reports, to a wide range of network abnormalities, allowing network administrators to quickly isolate specific issues, trends, or potential threats within a network, minimizing downtime or data breach.
Most problems display warning signs of some sort before becoming critical issues. If small problems can be identified and corrected early, there are less likely to have a chance to develop into larger problems.
The network monitoring process generates alerts and reports on issues that include denial-of-service attacks on key points in a network to rogue access points attempting to connect to the wireless infrastructure. The network monitoring process allows visualize the issues, root causes, and possible clues to fix an issue is crucial for the network administration teams.
The data collated by the network monitoring tools using standard protocols is displayed graphically to help admins use the information in managing a network in a streamlined way.
A network monitoring application collects and reports on a variety of data from all kinds of devices and nodes within a network. The collected data is filtered and analyzed to identify a variety of network problems. These network problems can include the following:
- Device failures
- Link outages
- Interface errors
- Packet loss
- Application response time
- Configuration changes
How affordable are the network monitoring tools?
There are many options for network monitoring in the market, which come with different price tags.
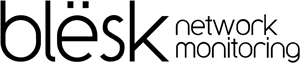
blësk is a comprehensive, intuitive, and yet the most affordable network monitoring solution to monitor a-z of a network.
It comes with the following 8 modules:
- Application Performance Monitor (APM)
- Network Performance Monitor (NPM)
- Network Traffic Analyzer (NTA)
- Event Log Manager (ELM)
- Switch Port Manager (SPM)
- Network Security Monitor (NSM)
- Network Configuration Manager (NCM)
- Asset Life Manager (ALM)
The most important modules of blësk for monitoring connected IoT devices are discussed below.
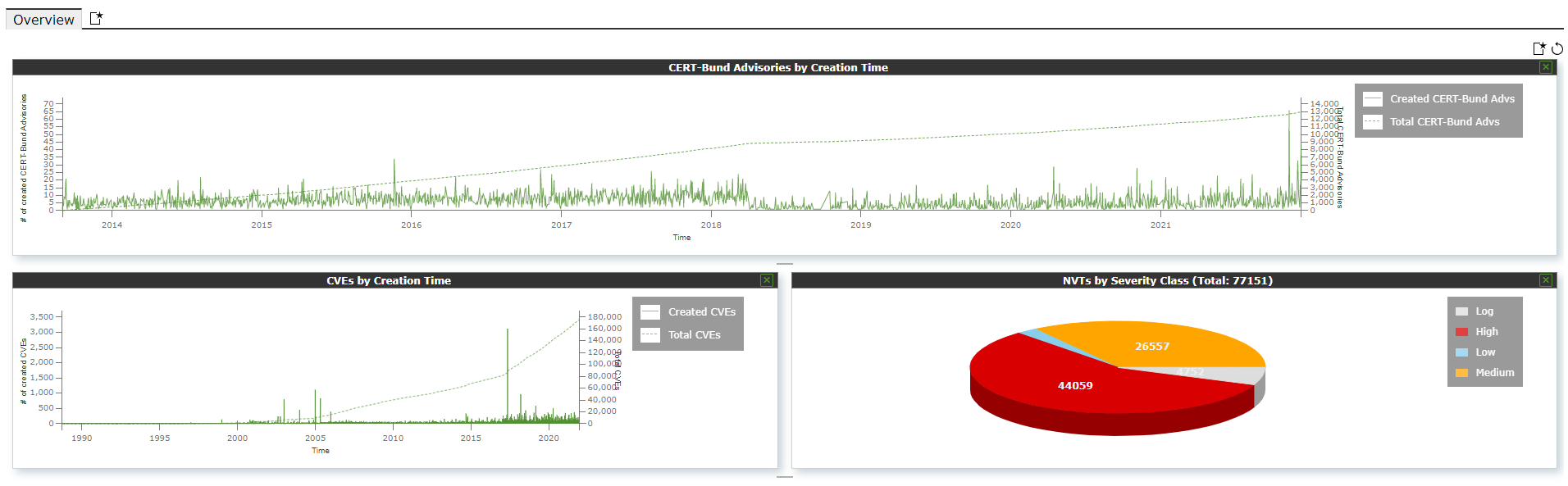
blësk Network Security Monitor (NSM)
blësk Network Security Monitor (NSM) function provides a way to continually identify potential vulnerabilities on systems and produces a detailed plan on how to remediate and remove those vulnerabilities from your critical business systems.
blësk NSM function allows to automatically scan a subnet of a network as per a custom schedule and automatically report the results to the administrator by email in a different format. blësk NSM module allows to define targets for vulnerability scan, which may be a single IP or range of IP addresses to execute NVT script towards the targeted system(s) to test for vulnerability and it allows to schedule the frequency of running the test. NSM module allows to create an infinite custom dashboard for group of devices for the ease of monitoring devices by device type.
Do not have resources? A managed service can be an option for you.
We understand that some organizations may don’t have the inhouse capacity to facilitate many essential tasks; therefore, blësk offers managed services to the low resourced organizations to monitor their network services.
Download a free trial of blësk at https://www.blesk.ca/free-trial/